Terminal operation security
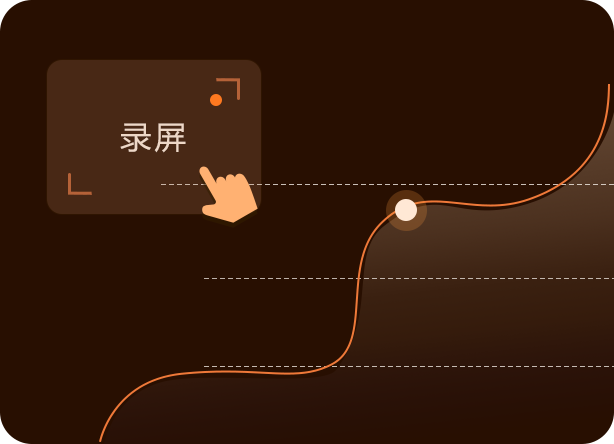
- Screen operation recording
- File operation record
- Document release monitoring
- Data tampering record
- Sensitive information monitoring
User behavior security
- Face authentication
- Mobile phone photo recognition
- Identify two persons in the same frame
- Identification of writing on a desk
- Recognition of personnel leaving their posts
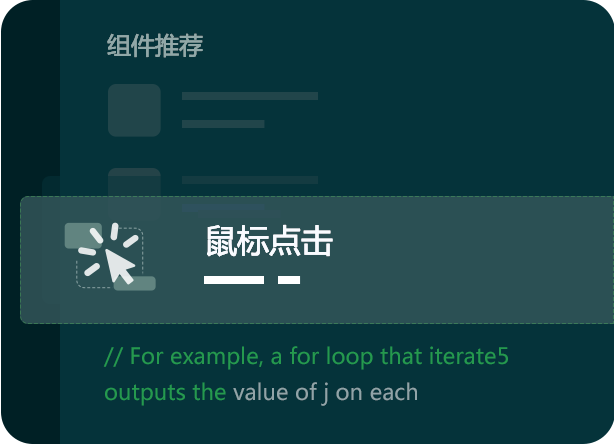
 Automation
Automation
 Bank
Bank
 Insurance
Insurance
 Logistics
Logistics